
Powerful data privacy and enhanced productivity for a leading KPO service provider
One of India’s largest BPO/KPO organizations needed to ensure the security of the highly sensitive healthcare data under their management.
Enforce consistent security standards across diverse devices and user groups through centralized policy controls. Streamline device onboarding while maintaining granular access restrictions tailored to organizational structure and compliance requirements.
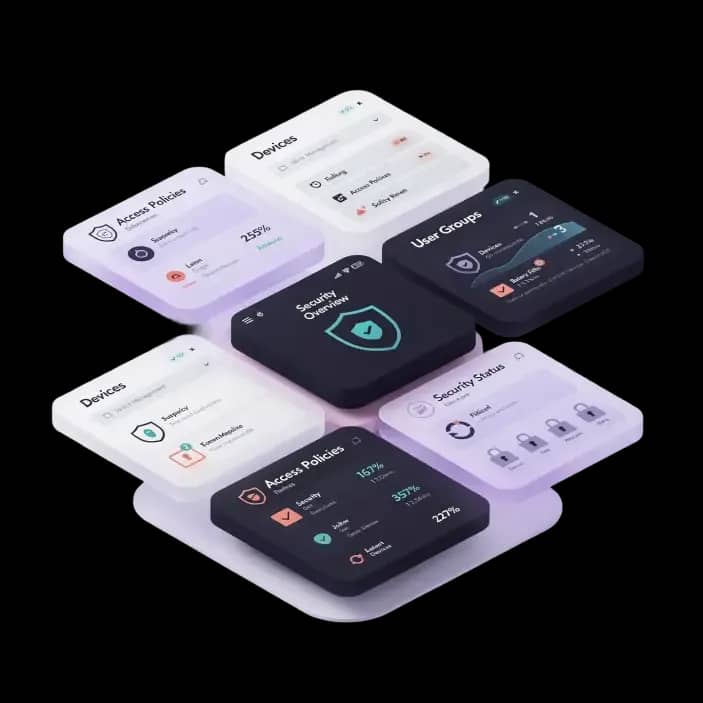
Enforcing policies across your organization’s devices involves centralizing IT administrative control over device onboarding, access permissions, and security features across platforms, ensuring only compliant devices gain corporate access while enforcing organization-specific policies through automated group-based controls.
Allow administrators to perform a complete wipe of user devices remotely. Securely erase device data if the device is lost or compromised.
Enable administrators to remotely remove only the work profile and corporate data without affecting personal content.