
Powerful data privacy and enhanced productivity for a leading KPO service provider
One of India’s largest BPO/KPO organizations needed to ensure the security of the highly sensitive healthcare data under their management.

Whichever security or privacy regulation you are working to comply with, you’ll face two key requirements setting up the necessary security and access controls, and maintaining records for audits. Akku addresses both these needs seamlessly.
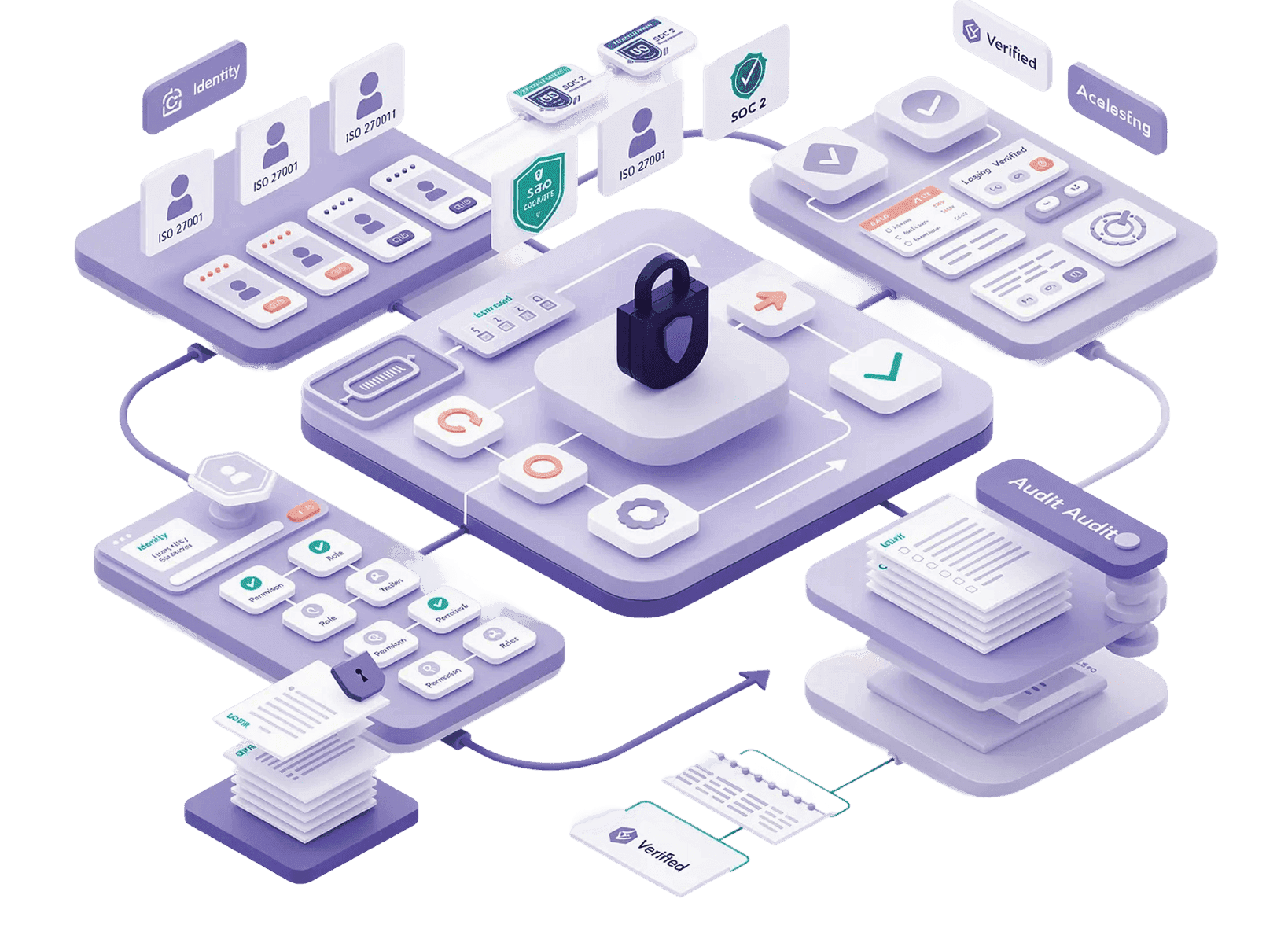
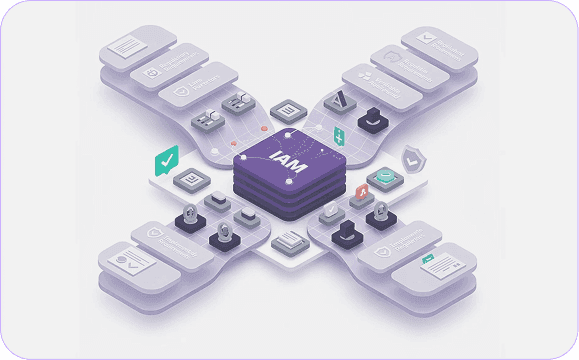

Different regulations have different needs and priorities when it comes to compliance. Whether your focus is on data privacy and user rights for GDPR, least privilege access for HIPAA, zero trust and continuous authentication for NIS2, or comprehensive reporting for DORA, the range of IAM features needed for compliance is wide ranging. Apart from controls, compliance also requires verifiable proof of measures taken in line with each regulation. Audits need hard evidence to validate your compliance - putting the measures in place isn’t enough by itself.
Akku provides you with the comprehensive IAM feature set you need to implement, besides maintaining comprehensive audit logs to help you demonstrate compliance during audits.

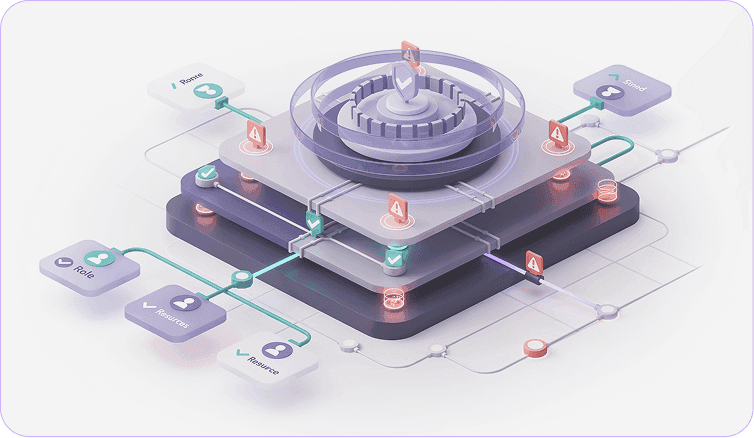
Exercise granular control over the level of access for each user, and ensure no user has excessive permissions - an important foundation to compliance with most data security and privacy regulations.
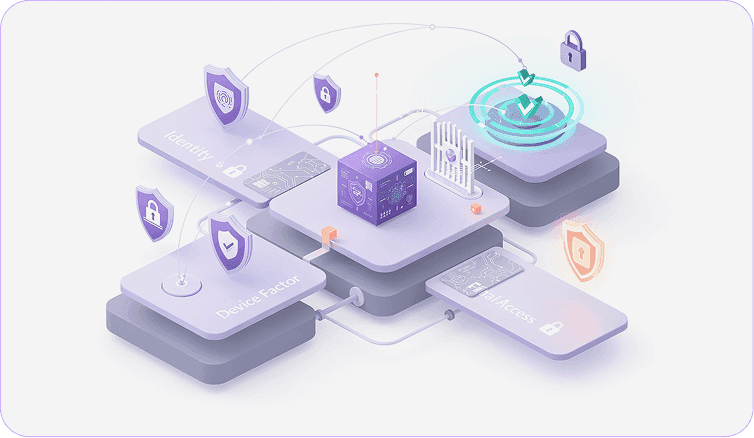
Reinforce identity verification and prevent unauthorized access with an additional authentication factor beyond your users’ passwords, including intelligent anomaly detection.
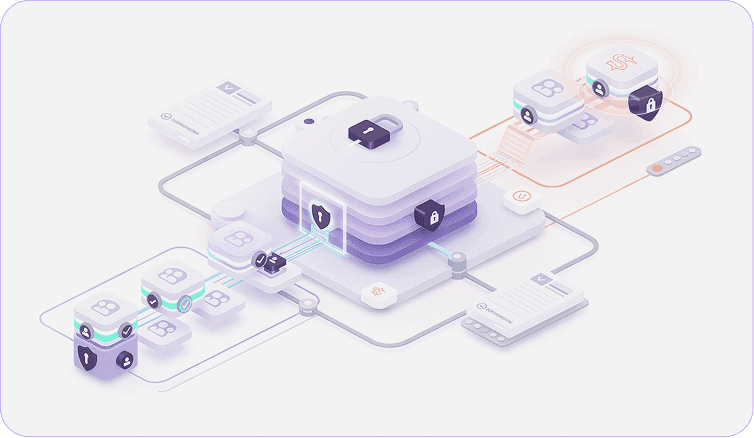
Experience certainty in the right permissions being assigned to each of your users at provisioning, and total revocation of access at de-provisioning.
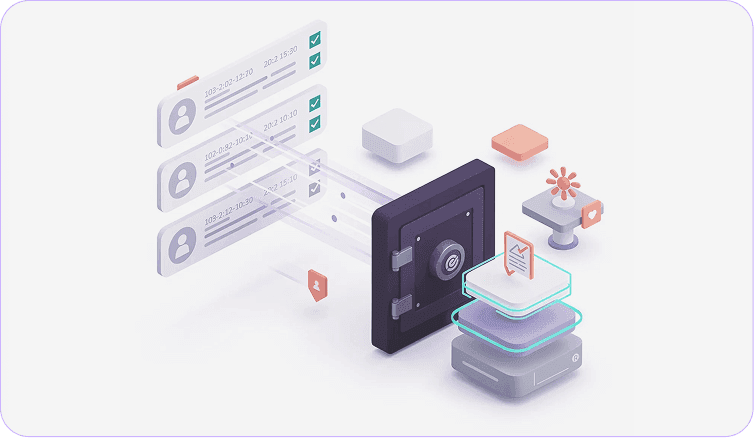
Maintain detailed logs of all access activity by every user to prove compliance with regulations during audits.